What is Black Hat SEO?

BlackHat SEO is the set of search optimization tactics that try to gain quick ranking wins by breaking search engine rules. This article explains what those tactics look like, why people use them, and what happens when sites get caught. Read on for clear examples, historic cases, modern practices, detection signals and ethical questions.
Defining BlackHat SEO
BlackHat SEO focuses on short-term gains instead of long-term value. People who use these techniques aim to trick search engines or manipulate ranking signals rather than build better pages for real users. The methods can work briefly, but they carry high risk.
Search engines publish webmaster guidelines and quality standards. BlackHat methods intentionally violate those rules. That contrast is the simplest way to tell BlackHat from legitimate, whitehat optimization strategies.
BlackHat strategies vary by technical skill and scale. Some are crude, like hiding keywords in tiny text. Others are sophisticated, like running large networks of fake sites to funnel link value. The common thread is that the intent is manipulation rather than helpful content.
Many operators hope to profit fast. They chase traffic, ad revenue, or affiliate clicks with risky shortcuts. That motive explains why BlackHat keeps appearing even as defenses get stronger.
Historic Examples and Modern Practices
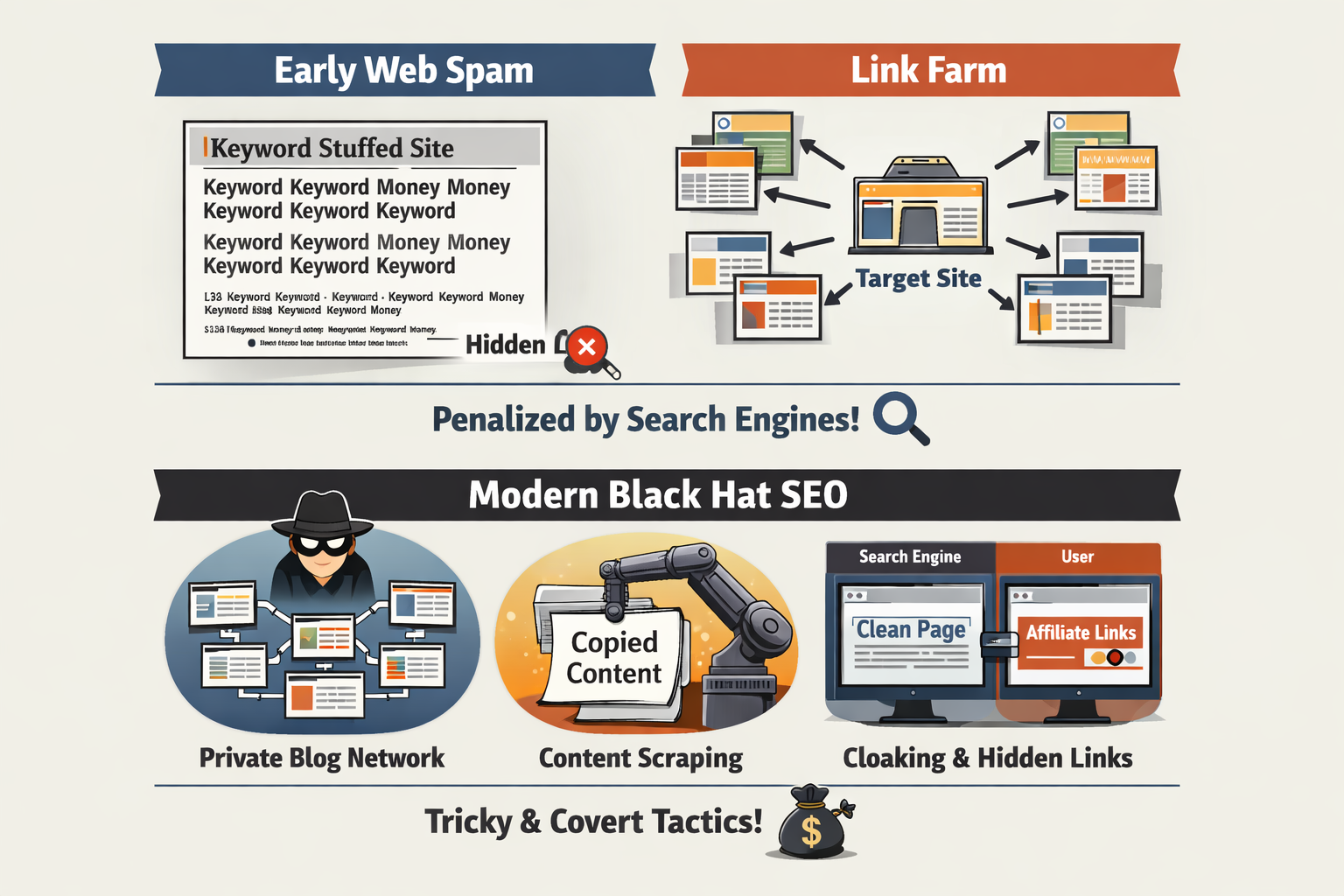
Early web spam was often obvious.
In the late 1990s and early 2000s, pages stuffed with keywords and hidden links were common. Those pages ranked well for a time, then search engines improved and penalized the offenders. Classic cases include sites whose visible content was gibberish but stuffed with targeted terms.
Link farms were another early approach.
Operators built clusters of low-quality pages linking to target sites to pass apparent authority. Search engines later built algorithms to discount or penalize such networks. Still, the idea did not disappear; it evolved.
Today, BlackHat techniques adapt to defenses.
People still buy links, but they may hide purchases through complex contracts or use private blog networks to mimic legitimate link profiles. Content scraping now uses automated tools that rewrite and slightly alter copy to evade simple duplicate-detection checks.
Modern cloaking can be technical: serving different HTML based on user-agent signals or using server-side logic. Some operators combine several tactics—scraped pages with hidden affiliate links and automated backlinks—to create a temporary cash machine. These modern practices are more covert, but the ethical and practical risks remain high.
How Search Engines Detect and Penalize
Search engines use a mix of automated detection, pattern analysis and manual review to find manipulative behavior. Algorithms look for unnatural link patterns, sudden traffic spikes, repeated content, and mismatches between user behavior and search rankings. These signals form the basis for penalties.
Algorithmic penalties often lead to ranking loss across many queries. Manual actions are targeted steps where a reviewer flags a site for policy violations. Either way, affected pages lose visibility and traffic. In severe cases, a site can be removed from the index for an extended time.
Detection has improved with machine learning models and large behavioral datasets. Yet the process is not perfect. False positives happen, and clever spammers sometimes evade filters for months. When a site is flagged, the recovery process can be complex and time-consuming.
Recovery usually requires identifying every abusive practice, fixing or removing problematic content, and submitting a thoughtful reconsideration request. That process can be costly and stressful—especially for businesses that rely on organic traffic.
Ethics, Reputation and Legal Risks
BlackHat SEO raises direct ethical questions. Manipulating search results harms users who expect relevant answers. It also undermines fair competition for businesses that play by the rules. The damage is both practical and reputational.
Legal risks exist too. Buying certain types of links can violate advertising disclosure laws or terms of service for platforms. Some BlackHat practices, such as impersonation or fraud, can cross into criminal behavior depending on local laws. That risk varies by tactic and jurisdiction, but it is real.
Reputational harm often outlasts ranking penalties. A company exposed for using deceptive tactics can lose customer trust. Restoring that trust takes careful work and transparent communication, not just technical fixes.
Ethical SEO professionals argue that long-term success is built on useful content, good user experience and genuine promotion. The short gains from BlackHat rarely justify the ongoing risks to brand and business stability.
How to Respond: Tasks for Site Owners and SEO Professionals
If you suspect a site is using BlackHat methods, prioritize clear steps to diagnose and remediate. Below are practical tasks to guide a response and recovery plan:
Audit backlinks: Gather your backlink profile and inspect for low-quality or paid links. Remove or disavow links that look manipulative.
Review on-page content: Check for hidden text, keyword stuffing, or duplicated material. Replace thin or scraped pages with original, helpful content.
Check technical cloaking: Verify server responses for different user-agents and ensure search engines and users see consistent content.
Fix site architecture: Remove doorway pages and redirects that exist solely for search engines. Consolidate thin pages into useful resources.
Document changes: Keep detailed records of fixes and removals so you can explain actions if you submit a reconsideration request.
These tasks need to be done thoroughly and honestly. Quick patches may not be enough if the underlying scheme was extensive. A careful audit prevents future issues and is the first step toward regaining trust with search engines.
For teams, assign clear ownership of each task and set deadlines. Recovery often requires coordination between content, technical and legal stakeholders. Treat the response as a serious remediation project.
Practical Examples: What People Did Then and Now
Historic example: In the early days, some webmasters created pages filled with repeated keywords, tiny font sizes and invisible links. Those pages sometimes ranked well until search engines adjusted. The technique was simple but effective for a while.
Historic example: Link farms once operated as centralized hubs that exchanged links with many sites. Owners built hundreds of pages designed solely to pass link value. When algorithms learned to detect these farms, those networks collapsed and many sites lost rankings.
Modern example: Private blog networks mimic legitimate content sites but exist only to pass link authority. Operators buy expired domains, rebuild superficially useful pages, and link to client sites. The setup is more sophisticated now, but the goal is the same as old link farms.
Modern example: Automated content networks use scripts to scrape sources and produce thousands of low-quality pages. These pages may include affiliate links or ads. They can generate ad revenue while evading naive duplicate content checks, but search engines have become better at spotting patterns.
Common BlackHat Techniques
Below is a clear list of widely used BlackHat tactics and short explanations so you can recognize them quickly:
Keyword stuffing: Repeating keywords unnaturally in content or meta tags to influence ranking. Historically, this looked like walls of repeated phrases, often with poor grammar and readability.
Hidden text and cloaking: Showing different content to search engines than to users. Operators once hid blocks of text using matching background colors or off-screen positioning.
Doorway pages: Creating thin pages optimized for specific queries that redirect users to another page. These pages exist mainly for search engines, not for users.
Link schemes: Buying links, participating in link farms, or using automated link networks to inflate backlink counts. Private blog networks (PBNs) are a modern version of this idea.
Content scraping and spinning: Copying content from other sites or automatically rewriting it to avoid detection. Scraped content was common in early web spam.
Automated queries and comment spam: Using bots to post links in comments, forums, or profiles to create backlinks at scale. This tactic creates noise rather than real engagement.
Each technique tries to create signals search engines consider when ranking. The signals are fake or distorted. That is why search engines respond with penalties when they detect the pattern.
Recognizing these signs quickly helps site owners act. Some issues can be fixed and recovered from. Others lead to long-term ranking loss or delisting.
Key Takeaways
BlackHat SEO offers tempting, fast results. Yet the patterns are risky and often short-lived. When detected, penalties can cause lasting harm to traffic, revenue and reputation.
Recognize common techniques such as keyword stuffing, cloaking, link schemes, content scraping and automated spam. Historic tactics evolved into modern, more covert versions, but the core intent remains manipulation rather than value creation.
Search engines detect abuse with algorithmic signals and manual review. Recovery is possible but requires careful auditing, remediation tasks and clear documentation. Legal and ethical concerns also matter and can affect a business beyond search rankings.
For sustainable success, focus on genuine content quality and user experience. Shortcuts can work briefly, but long-term growth depends on trust, relevance and a responsible approach to promotion.




